You’ve pushed a Group Policy change in Active Directory and need it applied on a client machine right now, not in 90 minutes when the background refresh finally kicks in! On Windows 10 and 11 (Pro, Enterprise, or Server), gpupdate /force is the command that does it.
gpupdate vs. gpupdate /force — What’s the Difference?
A plain gpupdate only downloads and applies settings that have changed since the last refresh. Adding /force re-downloads and re-applies every policy object, even ones that haven’t changed. Use /force any time you’re troubleshooting a policy that doesn’t seem to be sticking.
How to Force a Group Policy Update on Windows 10 and 11
Fix #1: Run gpupdate /force from an elevated terminal
This works on any domain-joined Windows 10 or 11 machine running Pro, Enterprise, or Education. You need an elevated (admin) prompt.
- Press
Windows + Xand select Terminal (Admin) or Command Prompt (Admin).
On Windows 10, you may see “Command Prompt (Admin)” instead of Terminal. - Click Yes if the UAC prompt appears.
- To force-refresh both computer and user policies at once, type the following and press Enter:
gpupdate /force
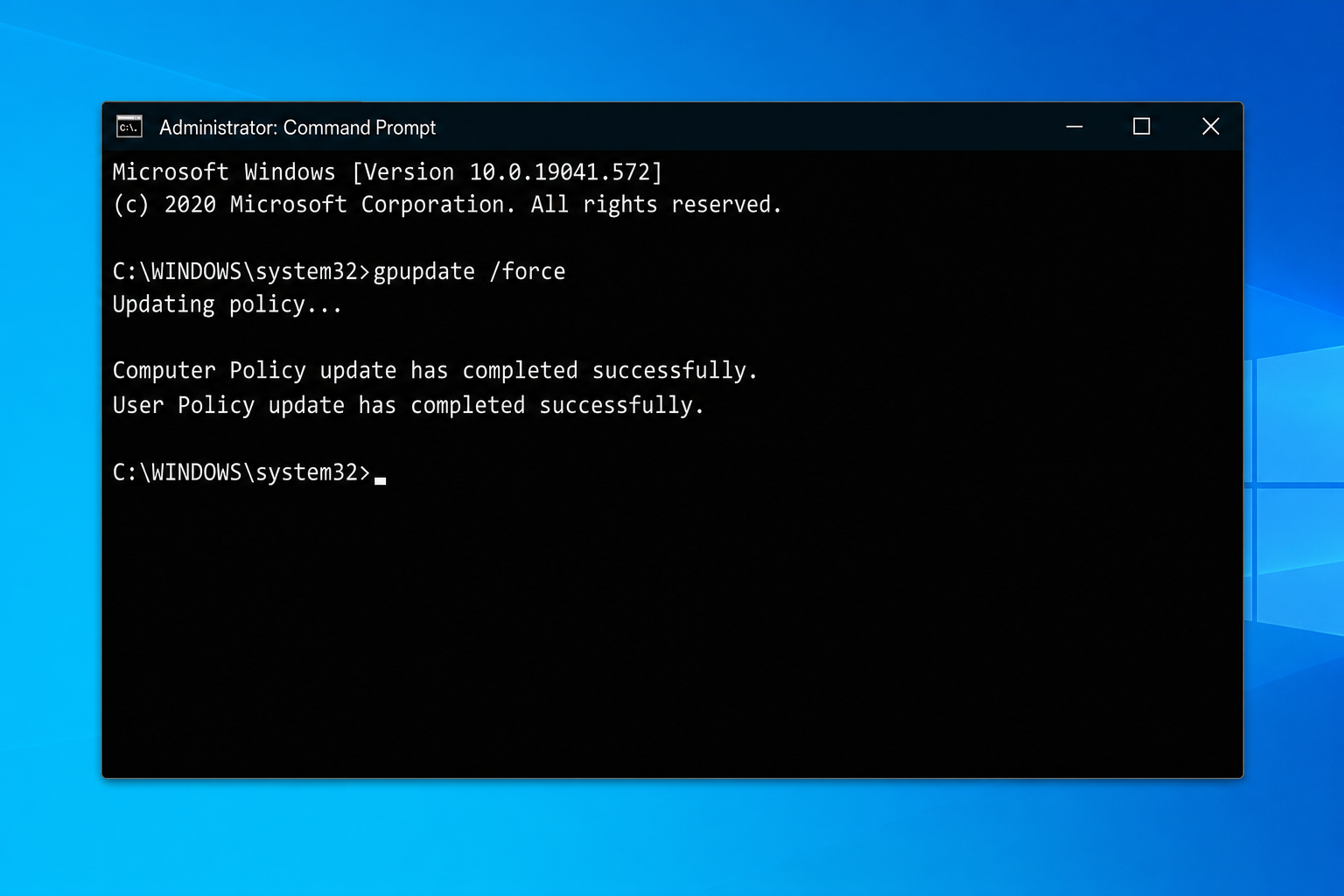
- Wait for the output to show:
Computer Policy update has completed successfully.User Policy update has completed successfully. - If prompted to log off or restart for certain policies to take effect, do so before testing.
If you only need to refresh one policy type, you can target it specifically:
- Computer policies only:
gpupdate /target:computer /force - User policies only:
gpupdate /target:user /force
Fix #2: Verify the policies actually applied with gpresult
Running gpupdate /force doesn’t guarantee every GPO applied cleanly. Use gpresult to confirm which policies are active on the machine.
- In the same elevated terminal, run:
gpresult /r
This prints a summary of applied Computer and User policies directly in the terminal. - For a full HTML report you can open in a browser, run:
gpresult /h C:\GPReport.html
Then openC:\GPReport.htmlin Edge or Chrome.
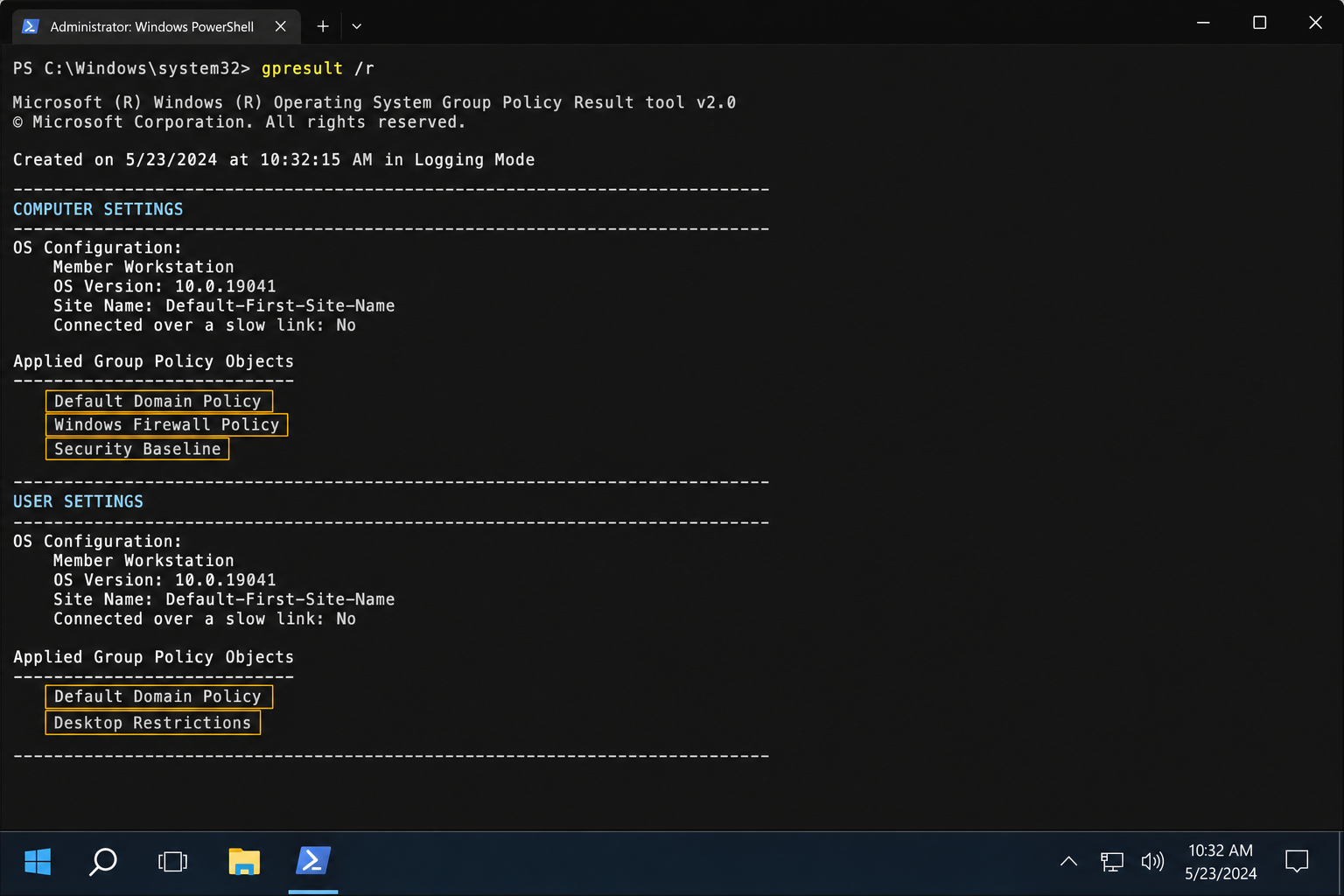
- Check the Applied Group Policy Objects section. If a policy you expected to apply is missing, it may be filtered, blocked by a higher-level GPO, or blocked by a WMI filter.
You can also open rsop.msc (Resultant Set of Policy) from Run (Windows + R) for a GUI view of every applied setting.
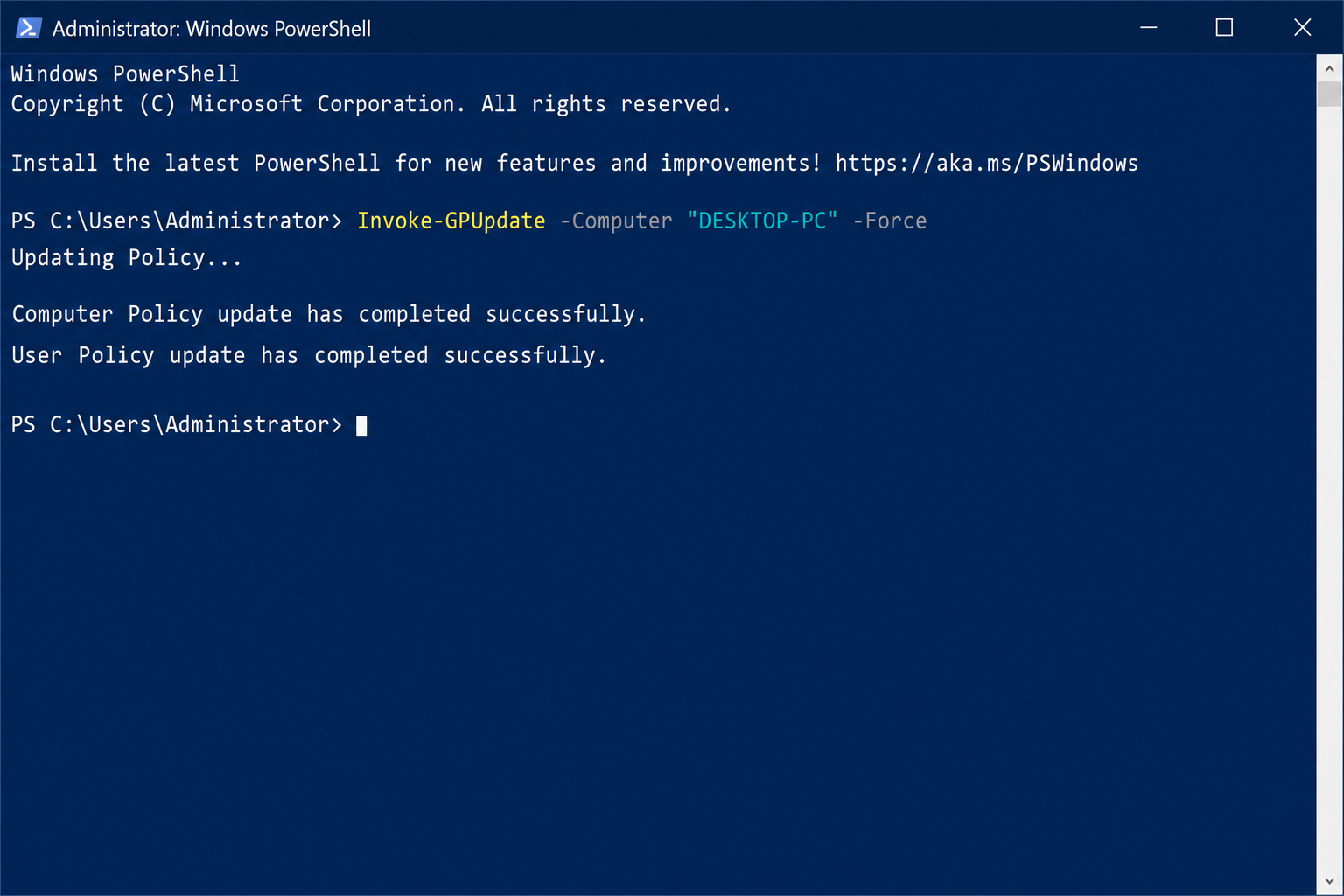
Fix #3: Force a remote Group Policy update with PowerShell (for IT admins)
If you need to push a policy refresh to a remote machine or a batch of machines without logging into each one, PowerShell’s Invoke-GPUpdate cmdlet handles this cleanly — no need to open inbound firewall ports manually through GPMC.
- On your domain controller or a management workstation with the RSAT Group Policy tools installed, open PowerShell as Administrator.
- To force-refresh a single remote computer, run:
Invoke-GPUpdate -Computer "COMPUTERNAME" -Force
ReplaceCOMPUTERNAMEwith the target machine’s hostname. - To push the update to every computer in an OU:
Get-ADComputer -Filter * -SearchBase "OU=Workstations,DC=contoso,DC=com" | ForEach-Object { Invoke-GPUpdate -Computer $_.Name -Force } - Confirm the update ran by checking the remote machine with:
Invoke-Command -ComputerName "COMPUTERNAME" -ScriptBlock { gpresult /r }
Fix #4: Fix policies that still won’t apply after gpupdate /force
If gpupdate /force completes without errors but the policy still isn’t taking effect, work through these checks in order:
- Check the time skew. Active Directory blocks policy application if the client’s clock is more than 5 minutes off from the domain controller. Run
w32tm /resyncin an elevated terminal to force a time sync, then trygpupdate /forceagain. - Check DC connectivity. Run
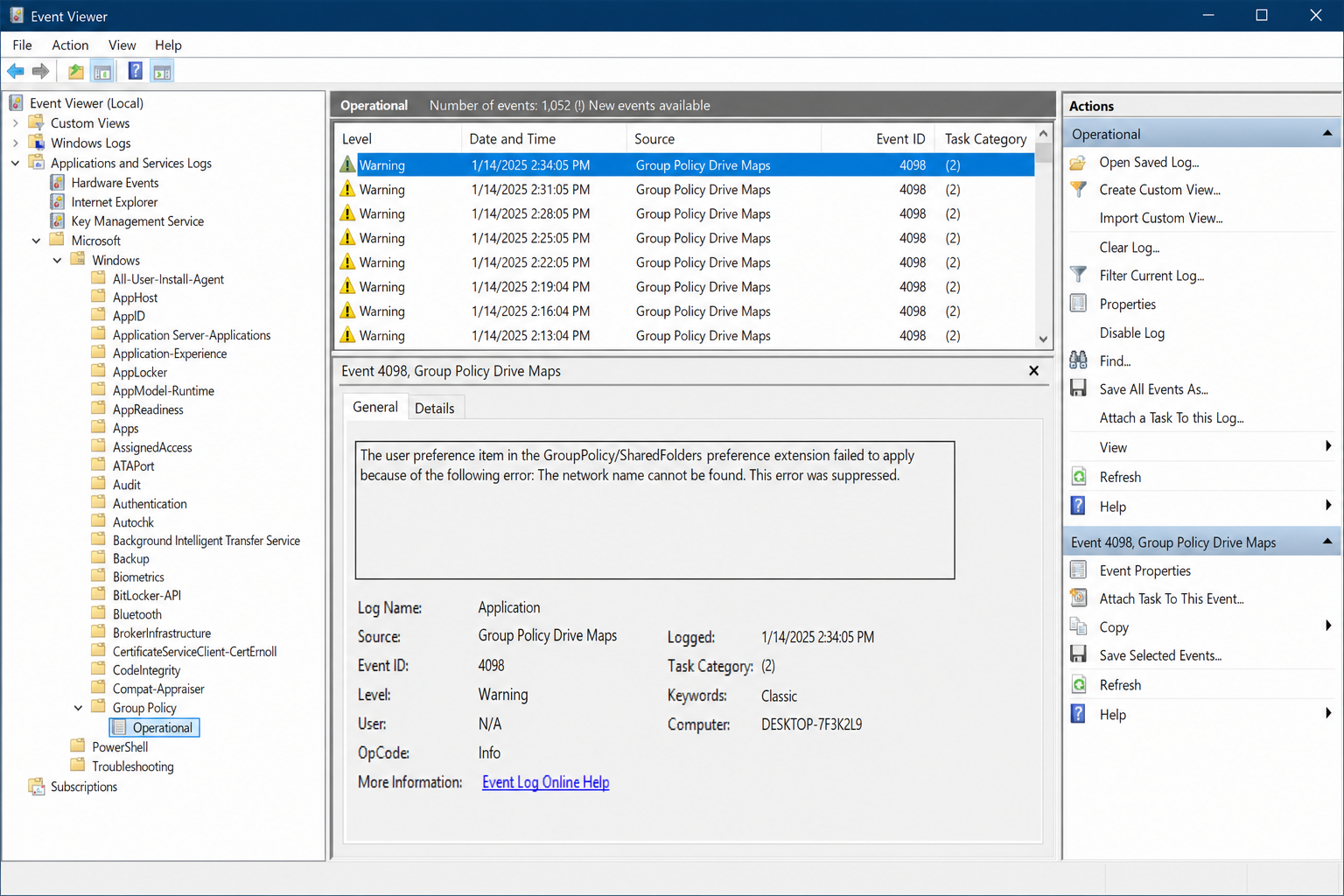
nltest /dsgetdc:YOURDOMAINto confirm the machine can reach a domain controller. A “no such domain” or timeout error means a network or DNS issue is blocking policy download entirely. - Check Event Viewer. Open Event Viewer > Applications and Services Logs > Microsoft > Windows > GroupPolicy > Operational. Error events here show exactly which GPO failed and why.
- Check for ADMX mismatches. If you’ve deployed Windows 11 policies but your central store on the DC still has Windows 10 ADMX files, those policies will silently fail. Download the latest ADMX templates from Microsoft and update your central store (
\\DOMAIN\SYSVOL\DOMAIN\Policies\PolicyDefinitions). - Reboot, don’t just log off. Some computer-side policies (especially startup scripts and software installation) only apply at boot, not at logon. A full restart after
gpupdate /forceis required for those.
What About Windows Home Edition?
Windows 11 Home and Windows 10 Home don’t include gpedit.msc or native Group Policy support. If your machine isn’t domain-joined, gpupdate will run but won’t apply any domain policies — there are none to apply. For local policy editing on Home editions, the free tool PolicyPlus is the closest alternative, though it’s primarily useful for standalone machines, not domain environments.
What About Intune and Modern Device Management?
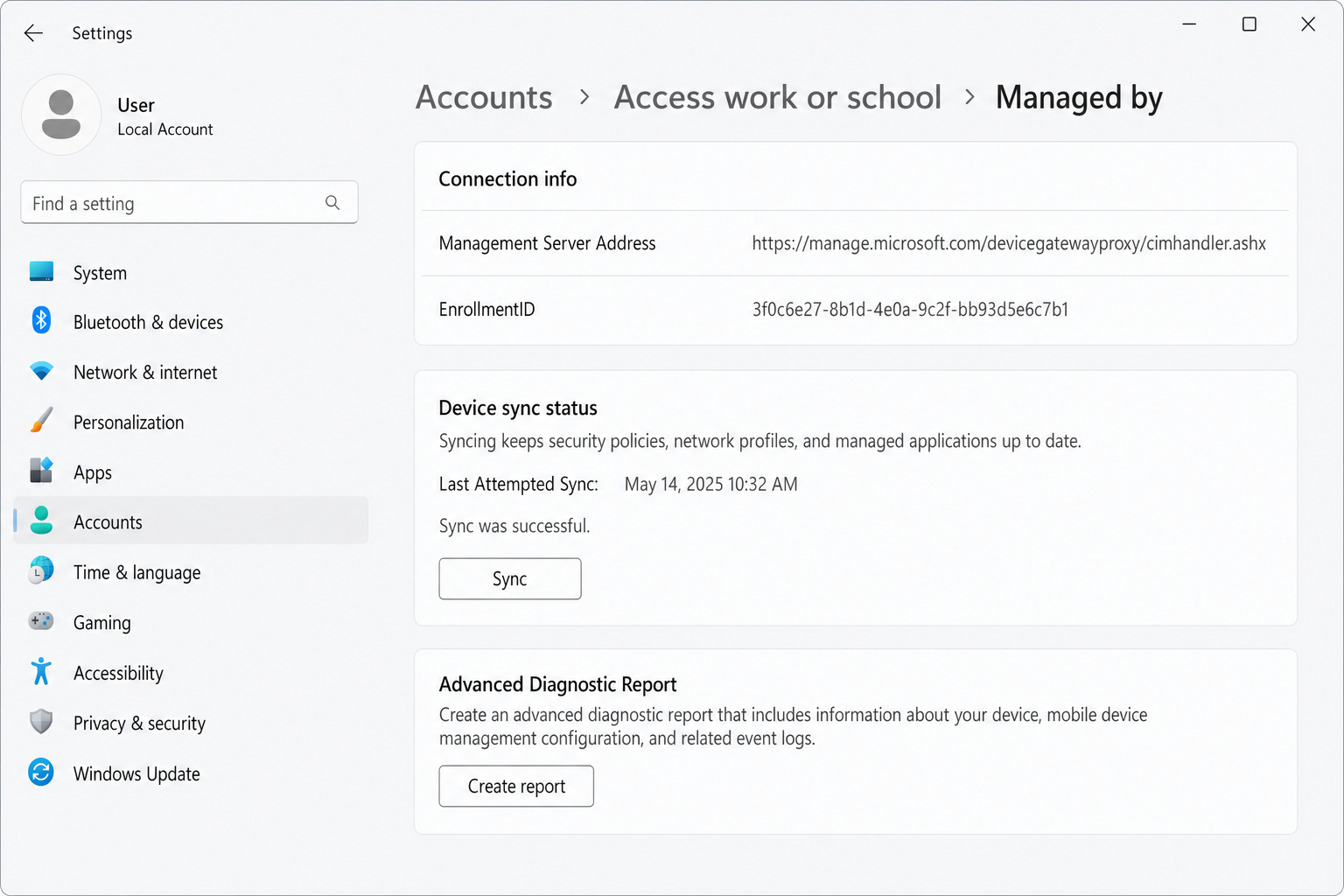
If your organization uses Microsoft Intune (Endpoint Manager) instead of or alongside traditional Group Policy, policies are delivered via MDM CSPs — not GPOs. gpupdate /force won’t trigger an Intune sync. To force a policy sync on an Intune-enrolled device, go to Settings > Accounts > Access work or school > click your account > Info > Sync. Applied Intune policies show up in Settings > Windows Update > Advanced options > Configured update policies, not in gpresult.
Conclusion
gpupdate /force in an elevated terminal handles the vast majority of “why hasn’t this policy applied yet?” situations — run it, wait for the success message, and reboot if prompted. If the policy still isn’t showing up after that, the gpresult /r output and the GroupPolicy Operational log in Event Viewer will tell you exactly what’s blocking it.