Why would you want to know how to block websites? Maybe you want to keep your kids safe on the Internet? Maybe you want to block distracting websites so you don’t procrastinate? It can also be used to block tracking sites that are embedded in ads.
Whatever your reason, you can simply block websites on Windows 10 using something called the hosts file.
The text below can get a bit technical, especially if you have never gotten into the nuts and bolts of Windows system files. If you want a quick overview, be sure to check out our short and easy to follow YouTube video first.
What Is The Hosts File?
Have you heard the term DNS (Domain Name System)? It refers to a system of files distributed around the Internet that help resolve domain names like helpdeskgeek.com into its actual Internet Protocol (IP) address which happens to be 13.225.198.106. That helps your computer know what server to talk to when you want to view this site.
Before DNS came into being in 1984, this was done through a local file on your computer called the hosts file. Back then computers weren’t connected to many other computers. At most, we may have connected to a few dozen. It was easy to keep all that information in a plain old text file. The host file lives on today.
How Does The Hosts File Work?
The hosts file allows the computer to look up other computer names, like localhost, or domain names, like helpdeskgeek.com and the IP number for them is right beside the name in the file. It’s a bit like how your friends’ names are associated with their phone numbers in your phone. You don’t need to remember or punch in the number, just find the person’s name.
Before we go further it’s important to understand that some IP addresses are reserved for local use. That means that they can only be used to point to your computer and devices within your immediate network. That means anything before your communication connects to the Internet.

For example, the IP address 127.0.0.1 always means the computer you’re working on, also known as localhost. Try typing that in your web browser. It will likely bring up a blank page.
Also understand that www.website.com and website.com are not the exact same thing. For both of them to take us to the same website both must resolve to the same IP address.
Blocking Websites With The Hosts File
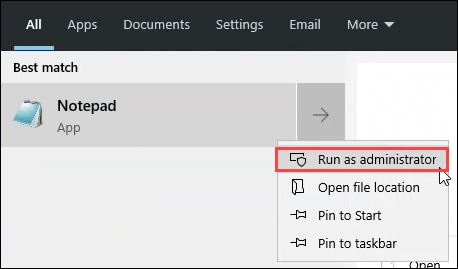
- Open Notepad as Administrator.
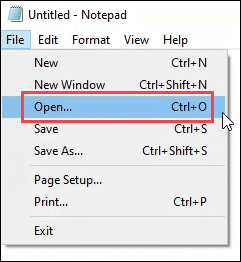
- Click on File > Open.
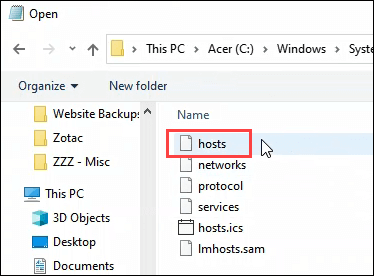
- Navigate to C:WindowsSystem32Driversetc
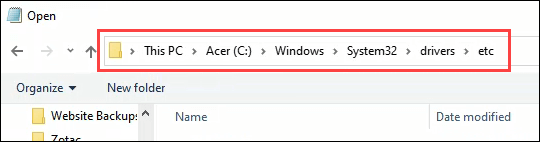
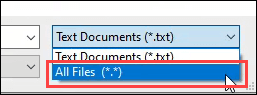
- Once there, change file type from Text Documents (*.txt) to All Files (*.*).
- Now you can see the hosts file. Open it.
- Go to the last line of the page and add your own line. Let’s say we’re blocking Facebook.
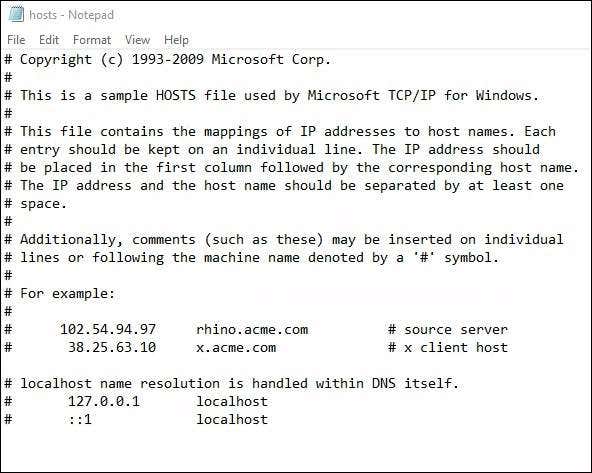
Enter the localhost IP of 127.0.0.1. Press the tab key and enter facebook.com. Press Enter to go to the next line. Create a second line like the one above, but use www.facebook.com instead of just facebook.com.

Is The Website Blocked?
Open the command prompt and run ping facebook.com then run ping www.facebook.com. You should see that the IP address it’s trying to ping is 127.0.0.1.
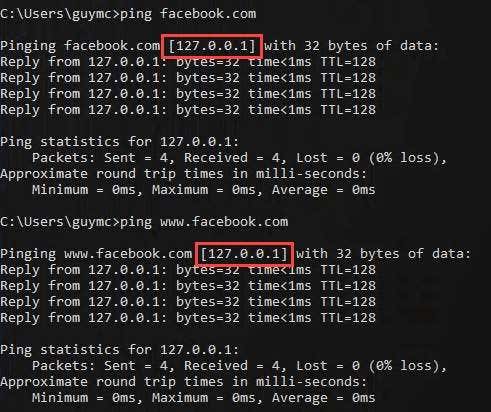
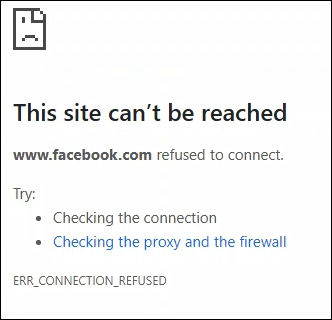
Now open your web browser and go to facebook.com. It might still load! Why? Facebook’s real IP may still be sitting in the browser cache and the browser will use that IP first. Delete your browser’s cache and try Facebook again. You should now see an error page.
I Don’t Want to See an Error Page
You could try redirecting the site to another IP address, but these days that won’t work well. Maliciously editing the hosts file used to be a common attack by hackers. Now, web browsers check carefully for certificates to prevent this. But, you can still try.

Another way to not see an error page is to install and set up a web server on your computer and have the hosts file point to that. Maybe have it display a page that says, “Get back to work!” or lists some of your goals as motivation to stay off social media.
What Else Can I Do With The Hosts File?
You can use the same technique but paste in the URLs of various malware and tracking ad sites. There is a pre-made hosts file of malware and ad sites that you can copy and paste into your hosts file. As of writing this, it was last updated in March, 2020.

