Microsoft says Windows Recall is “secured by Windows Hello” and security researchers released a tool called TotalRecall Reloaded that can read your entire Recall database without your PIN or face scan. Both are true, and here’s what to do about it.
Note: Windows Recall is available only on Copilot+ PCs running Windows 11. If your PC doesn’t carry the Copilot+ designation, Recall isn’t installed and none of this applies to you. Check at Settings > System > About. Not sure? See our guide on how to check if your PC is a Copilot+ PC.
What Windows Recall Actually Does
Recall is an opt-in feature on Copilot+ PCs. It periodically screenshots your screen and runs those images through an on-device AI model to make them searchable. Think of it as a photographic memory for your PC: type “that mortgage article I was reading last Tuesday” and Recall surfaces the exact snapshot. Everything stays on your device.
That database is where the security conversation starts. It may contain screenshots of banking portals, passwords you typed into forms, private messages, and medical records. That’s what makes it a meaningful target.
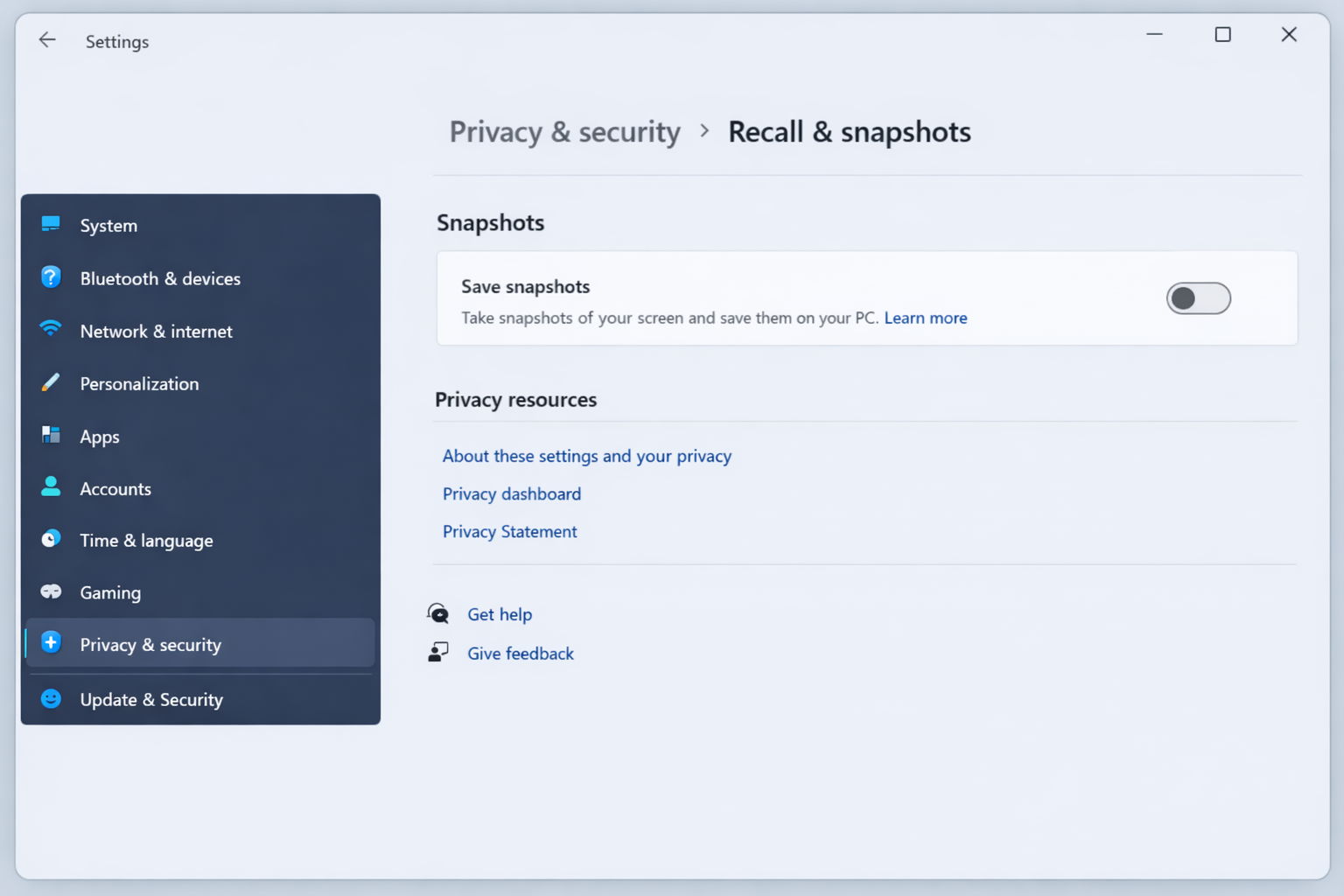
As of 2026, Recall is opt-in during Windows 11 setup on Copilot+ PCs. Enable or disable it anytime at Settings > Privacy & Security > Recall & Snapshots.
26H1 update: With Windows 11 26H1, Recall availability has expanded to additional Copilot+ devices beyond the original launch lineup. The feature remains opt-in on all supported hardware. If you recently received a new Copilot+ PC or a 26H1 update, check Settings > Privacy & Security > Recall & Snapshots to confirm your current Recall status.
The “Just in Time” Decryption Model, Explained Simply
The Recall database is encrypted when your PC is off, locked, or signed out. Think of it like a safe that locks itself when you leave the room. The moment you log back in, Windows automatically unlocks that safe in the background – no second PIN prompt, no face scan, no extra step. Microsoft built it this way to keep things fast and frictionless.
That automatic unlocking is the detail that matters for everything that follows.
What Microsoft’s Security Claims Actually Cover
Microsoft’s “protected by Windows Hello” language is accurate. It just covers a specific slice of the picture. Here’s what it genuinely protects against:
- Stolen or extracted drives. If someone removes your SSD and plugs it into another PC, the Recall database is encrypted and unreadable without your credentials. That’s real protection.
- Remote attackers. A hacker trying to reach your PC over the internet can’t access your Recall data without getting past Windows Hello first.
- Unauthorized logins. Someone who doesn’t know your PIN and can’t pass face recognition can’t log in and can’t reach the database.
- Other user accounts on the same PC. Recall data is scoped to the account that generated it. A separate Windows account can’t read another account’s snapshots.
“Encrypted at rest” is real protection. It covers scenarios where your PC is off, locked, or being accessed from outside your account. What it doesn’t cover is what happens after you’re already logged in and Recall has already decrypted the database in the background.
The key distinction: “protected by Windows Hello” describes the barrier to entering your account. It says nothing about what programs or people can do once they’re already inside your active session.
What TotalRecall Reloaded Actually Found
TotalRecall Reloaded is a proof-of-concept tool that was built to demonstrate a specific security gap, not to be used maliciously. What it showed: any program running under your Windows user account can open and read the Recall snapshot database without re-entering your PIN or face scan.
In practical terms, that means three things:
- Malware running under your account — the kind triggered by a phishing email or a sketchy download — can read everything Recall has recorded.
- Anyone who sits down at your unlocked PC can browse your Recall history without knowing your password.
- Any application you run yourself has the same access, which is why the database can be queried without the official Recall interface.
This is not a remote exploit. The attacker or malicious program must already have access to your running Windows account. Locked PC, powered-off PC, no credentials, the database stays encrypted. TotalRecall Reloaded is a local access issue only.
“But Malware Could Already Do Damage Anyway”
Fair point. If malware is running under your account, it can already read your files and capture keystrokes. The reason Recall changes the calculation is scale and efficiency. Instead of watching your screen in real time or digging through individual files, an attacker gets a single searchable database containing months of screen activity, including banking sessions, typed passwords, private conversations, work documents, etc, all queryable in seconds. Recall doesn’t create a new category of risk. It concentrates existing risk into one very convenient target.
Who Is Actually at Risk
Before jumping to fixes, be honest about your actual situation.
Higher-risk profiles:
- You share a PC with others using the same Windows account
- You’ve downloaded software from unofficial sources, torrent sites, or run cracked applications
- You’ve clicked a suspicious link recently and aren’t certain nothing executed
- Your PC holds client data, financial records, HR files, legal documents, or medical information
- You use Recall on the same machine where you do online banking or manage business credentials
Lower-risk profiles:
- You’re the only person who uses your PC and it’s physically secure
- You don’t download from unofficial sources and Windows Defender definitions are current
- You’ve never enabled Recall, or you’re on a non-Copilot+ PC
- You practice solid security hygiene: unique passwords, phishing awareness, no suspicious attachments
For most careful home users, the risk is real but not urgent. The goal is reducing unnecessary exposure, not treating your PC like it’s under active attack.
How to Protect Your Windows Recall Data: Six Fixes, Simplest First
Fix #1: Restrict What Recall Is Allowed to Capture
This is the lowest-friction step and the right place to start. Recall has built-in filtering that lets you shrink the amount of sensitive data it ever records.
- Open Settings > Privacy & Security > Recall & Snapshots.
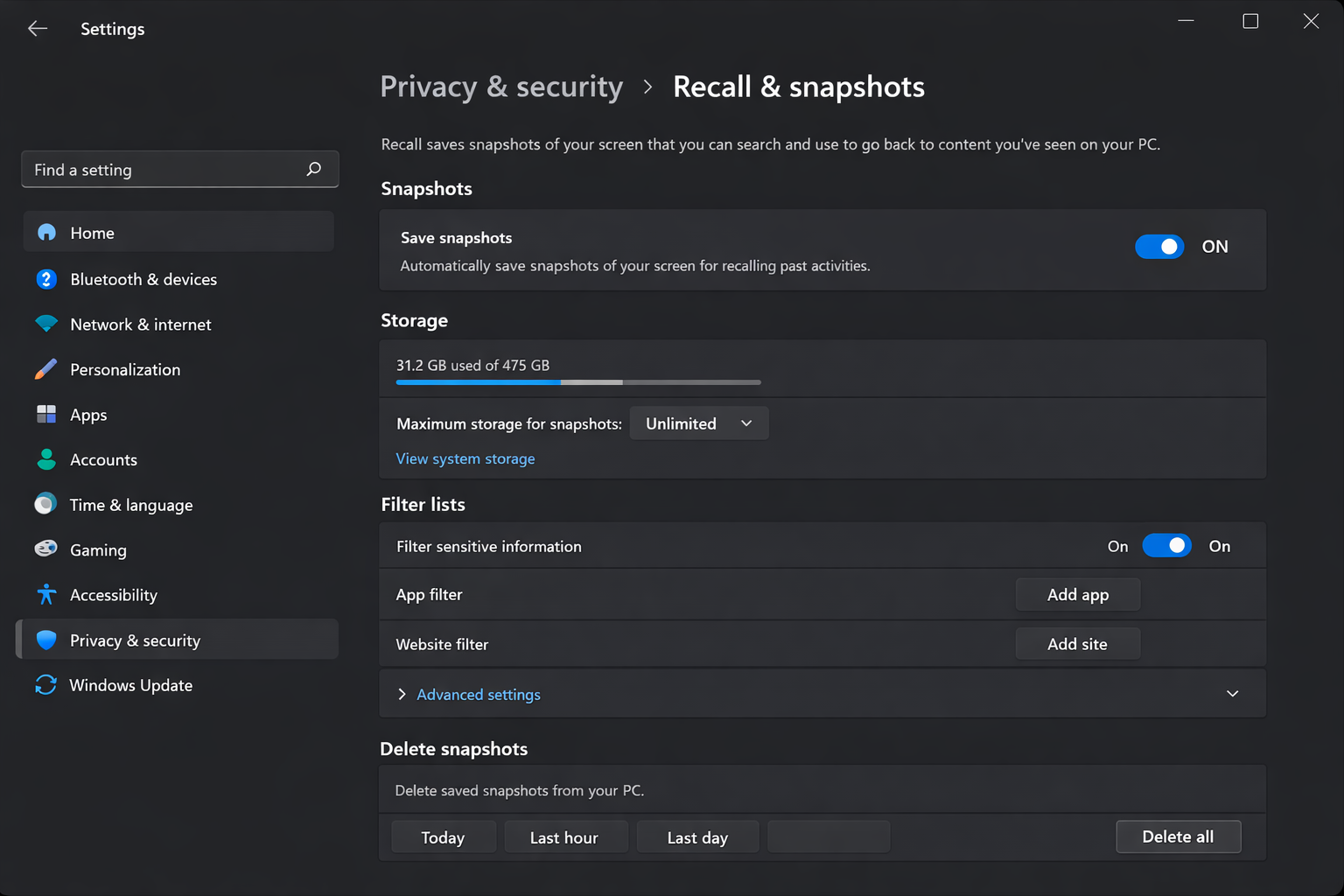
- Scroll to the Filter sensitive content or Excluded apps section (the label varies slightly by Windows build).
- Click Add an app and select any application you don’t want Recall to screenshot. Banking apps, password managers, and healthcare portals are the obvious candidates.
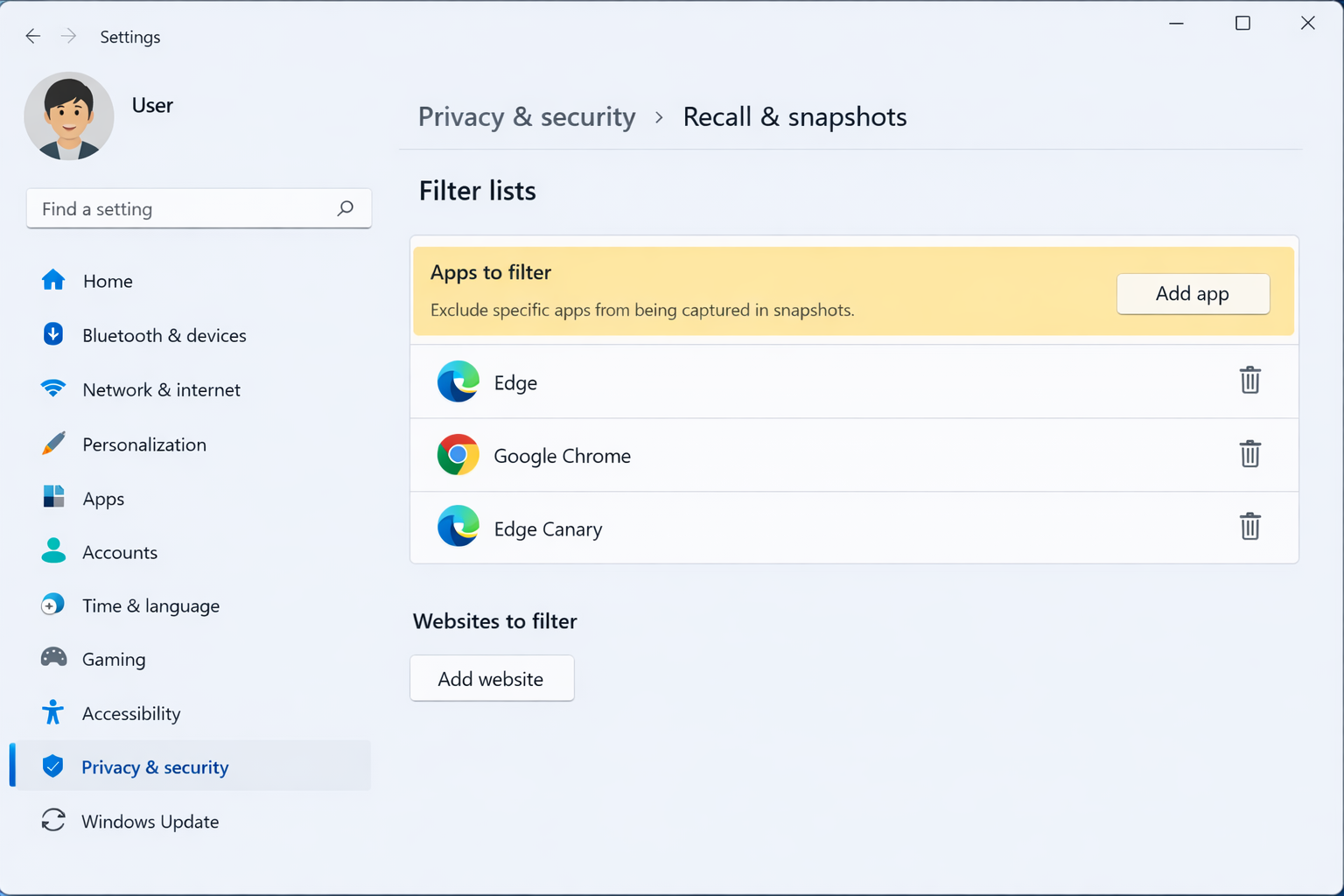
- Scroll back up and confirm Filter out private browsing activity is toggled on. This tells Recall to skip screenshots of InPrivate (Edge), Incognito (Chrome), and private (Firefox) windows. It should be on by default, but verify it anyway.
Limitation: This shrinks what’s in the database but doesn’t change the fact that whatever is stored remains readable by anything running under your account. You’re making the target smaller, not locking it.
Fix #2: Pause Recall During Sensitive Tasks
Pausing Recall stops new screenshots from being taken. It doesn’t delete your history or change any permanent settings. Use it when you’re about to do something you definitely don’t want recorded.
- Open Settings > Privacy & Security > Recall & Snapshots.
- Toggle Save snapshots to Off.
- Complete your sensitive task – tax filing, banking session, HR review, medical portal access.
- Return to the same Settings page and toggle Save snapshots back to On when you’re done.
Good candidates for pausing: online banking, tax software, password manager setup, any session involving client data or credentials.
Limitation: This only protects data going forward from the moment you pause. It does nothing for snapshots already in the database. For that, see Fix #3.
Fix #3: Delete Your Existing Snapshot History
Turning off Recall or adding filters doesn’t erase what’s already been recorded. Deleting your history removes the data that tools like TotalRecall Reloaded would actually target. Do this before applying any other fix and start from a clean slate.
- Open Settings > Privacy & Security > Recall & Snapshots.
- Scroll to the Delete snapshots section and click Delete snapshots.
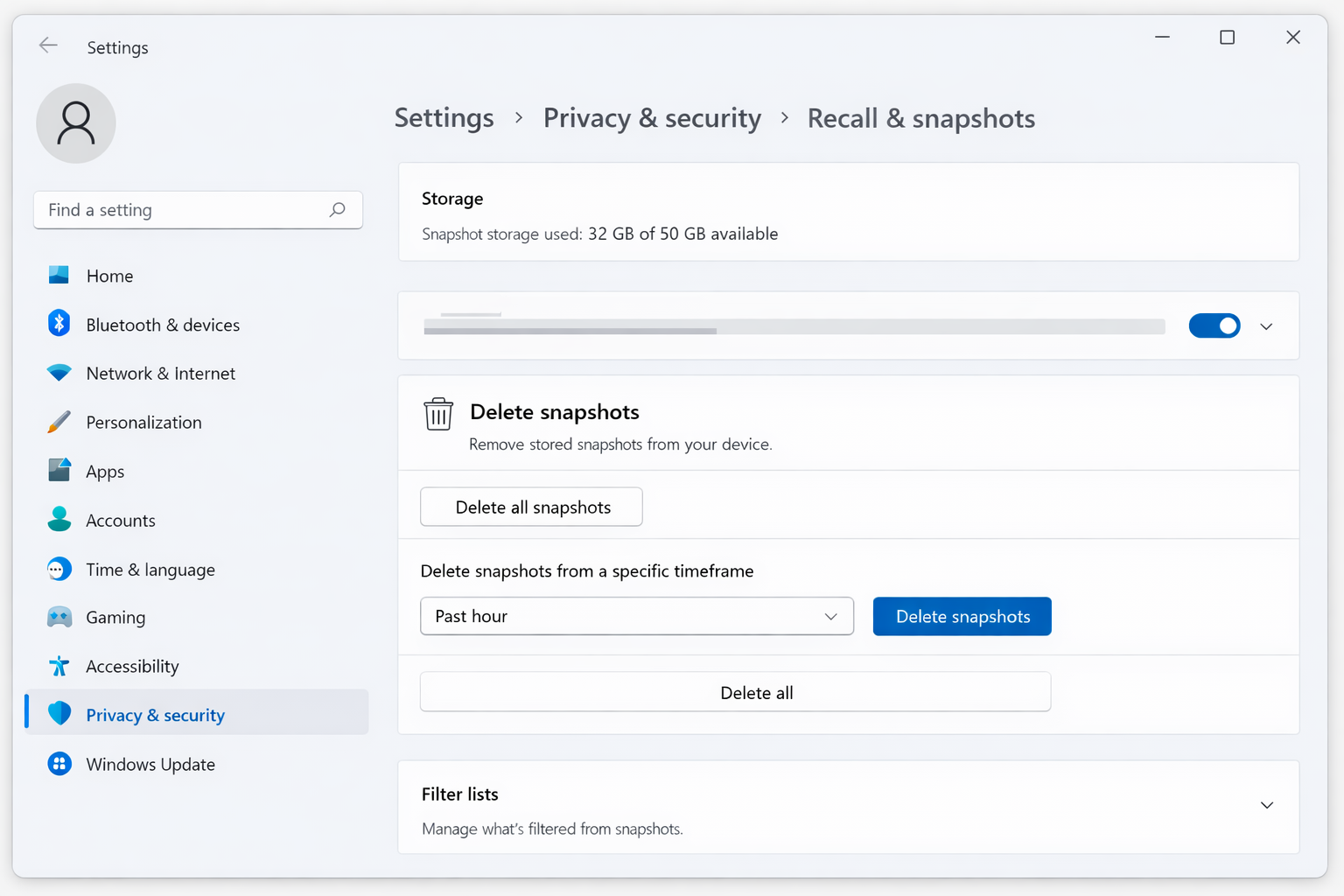
- Choose your deletion scope:
– Delete all removes the entire database, the most thorough option.
– Delete by date range removes snapshots from a specific period, useful if you want to keep older history but wipe a recent sensitive session.
– Delete by app removes snapshots tied to a specific application.
- Confirm the deletion when prompted. Windows Hello authentication may be required.
Limitation: This removes existing data but does nothing to prevent new sensitive data from accumulating if Recall stays active. Combine with Fix #1 or Fix #4 for ongoing protection.
Fix #4: Turn Off Recall Completely
If you share your PC, handle sensitive professional data, or aren’t confident in your security hygiene, turning Recall off is the cleanest answer. No database means nothing to extract.
- Open Settings > Privacy & Security > Recall & Snapshots.
- Toggle Save snapshots to Off, or click Turn off if your Windows build shows a dedicated disable option.
- Turning off Recall stops new captures immediately, but your existing snapshot history is retained. Follow the Fix #3 steps to delete that history now.
Recall is fully reversible — re-enable it anytime from the same Settings page. Turning it off doesn’t affect any other Windows features.
If you find Recall genuinely useful, that’s worth weighing. But for shared PCs and anyone with sensitive professional data, Fix #4 is the right call.
Limitation: This eliminates the Recall-specific risk but doesn’t address what else is accessible under your account if malware runs. Fix #5 handles that root condition.
Fix #5: Create a Separate Standard User Account for Daily Use
This fix addresses the underlying condition that makes the TotalRecall Reloaded finding possible. Recall data is tied to the Windows account that generated it. A Standard User account that Recall was never active under has no snapshot database at all.
There’s a broader benefit too. Running day-to-day as a Standard User instead of an Administrator means malware has significantly less ability to make system-wide changes, install drivers, or modify protected files. It’s a real security improvement, not just a Recall fix.
- Open Settings > Accounts > Family & other users.
- Under Other users, click Add account (or Add someone else to this PC depending on your Windows build).
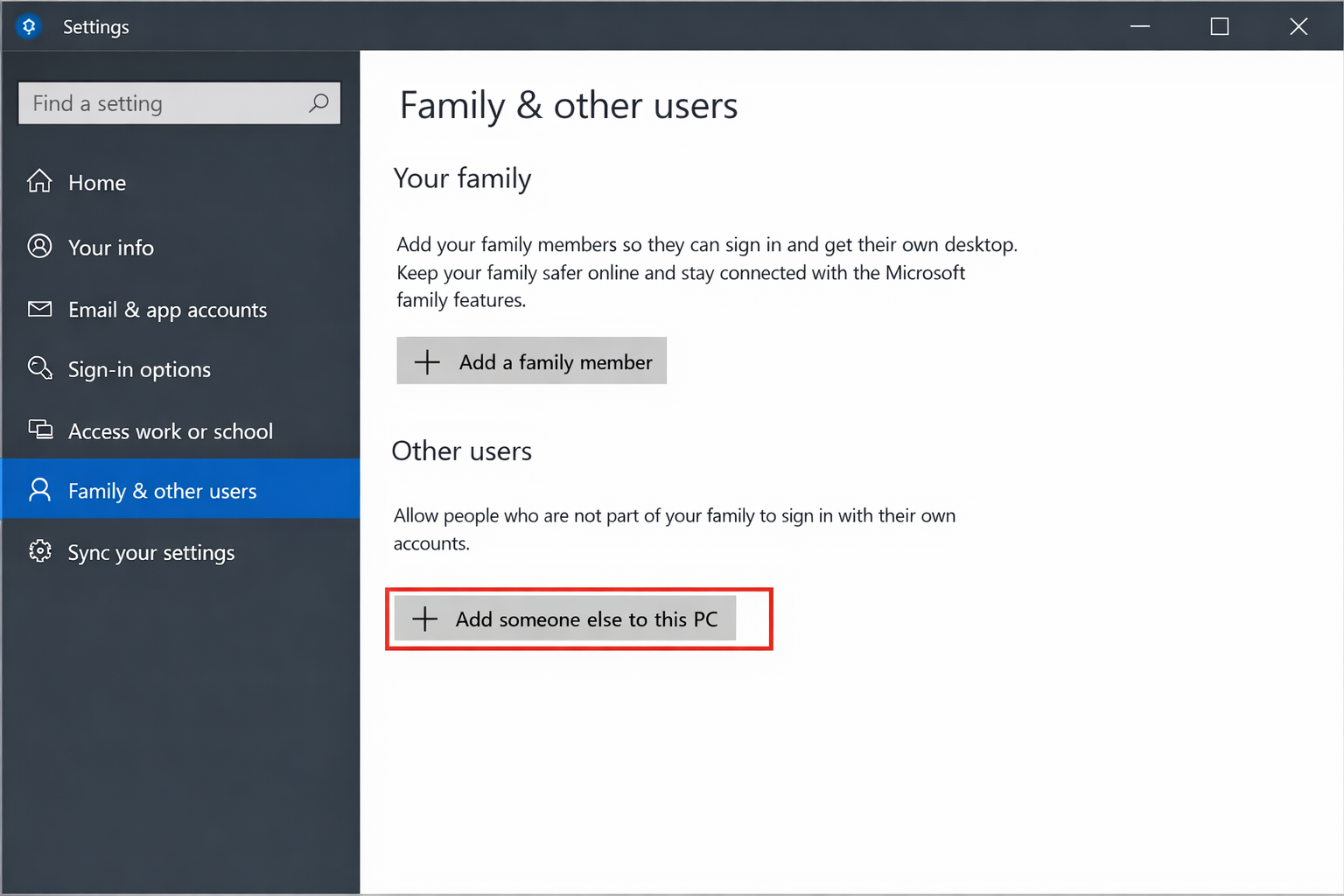
- In the account creation dialog, select I don’t have this person’s sign-in information, then Add a user without a Microsoft account to create a local account. Give it a name and a strong password or PIN.
- After the account is created, it appears under Other users as Administrator by default. Click the account name, click Change account type, set it to Standard User, and click OK.
- Sign out of your current account and sign in to the new Standard User account.
- From the Standard User account, enable Recall if you want it via Settings > Privacy & Security > Recall & Snapshots, and configure your filters (Fix #1) from scratch.
Keep your Administrator account for software installations and system changes. Use the Standard User account for everything else.
Limitation: Some tasks require Administrator credentials, so you’ll occasionally need to switch accounts or enter Admin credentials when prompted. This fix is best suited for users who handle sensitive data regularly and want the strongest structural protection.
Fix #6: Use Windows Defender Controlled Folder Access to Block Unauthorized Database Reads
Controlled Folder Access is a Windows Security feature that prevents unauthorized applications from reading or modifying files in folders you designate as protected. The Recall snapshot database lives under your user profile’s AppData folder — specifically at %LOCALAPPDATA%\CoreAIPlatform.00\UKP\ (the exact subfolder name is a unique identifier that varies per device). Adding your AppData path to Controlled Folder Access puts an extra access-control layer around the database.
Path note: The
%LOCALAPPDATA%\CoreAIPlatform.00\path is consistent with current 2026 Recall builds, but Microsoft may adjust folder naming in future Windows updates. If you don’t find this folder, paste%LOCALAPPDATA%into the File Explorer address bar and look for a folder beginning withCoreAIPlatformto confirm the correct name on your device.
This fix is best suited for technically confident users who want to keep Recall enabled and layer meaningful additional protection around it.
- Open the Start menu and search for Windows Security. Open it.
- Click Virus & threat protection in the left panel.
- Scroll down to Ransomware protection and click Manage ransomware protection.
- Under Controlled folder access, toggle it to On.
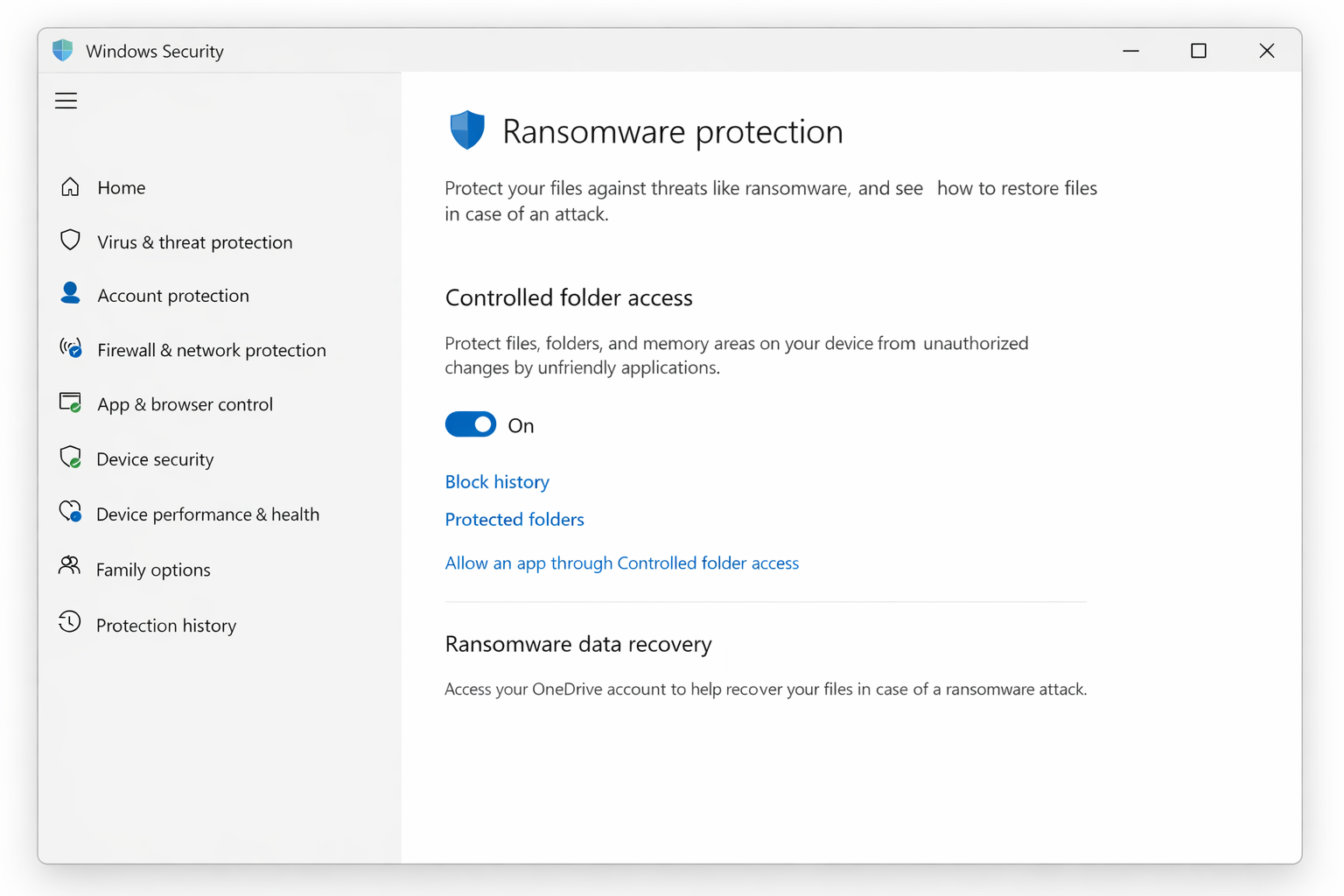
- Click Protected folders, then + Add a protected folder.
- Navigate to
%LOCALAPPDATA%\CoreAIPlatform.00\and add that folder. (Paste%LOCALAPPDATA%\CoreAIPlatform.00\directly into the File Explorer address bar to get there.) - Click Allow an app through Controlled Folder Access to manage your allowlist.
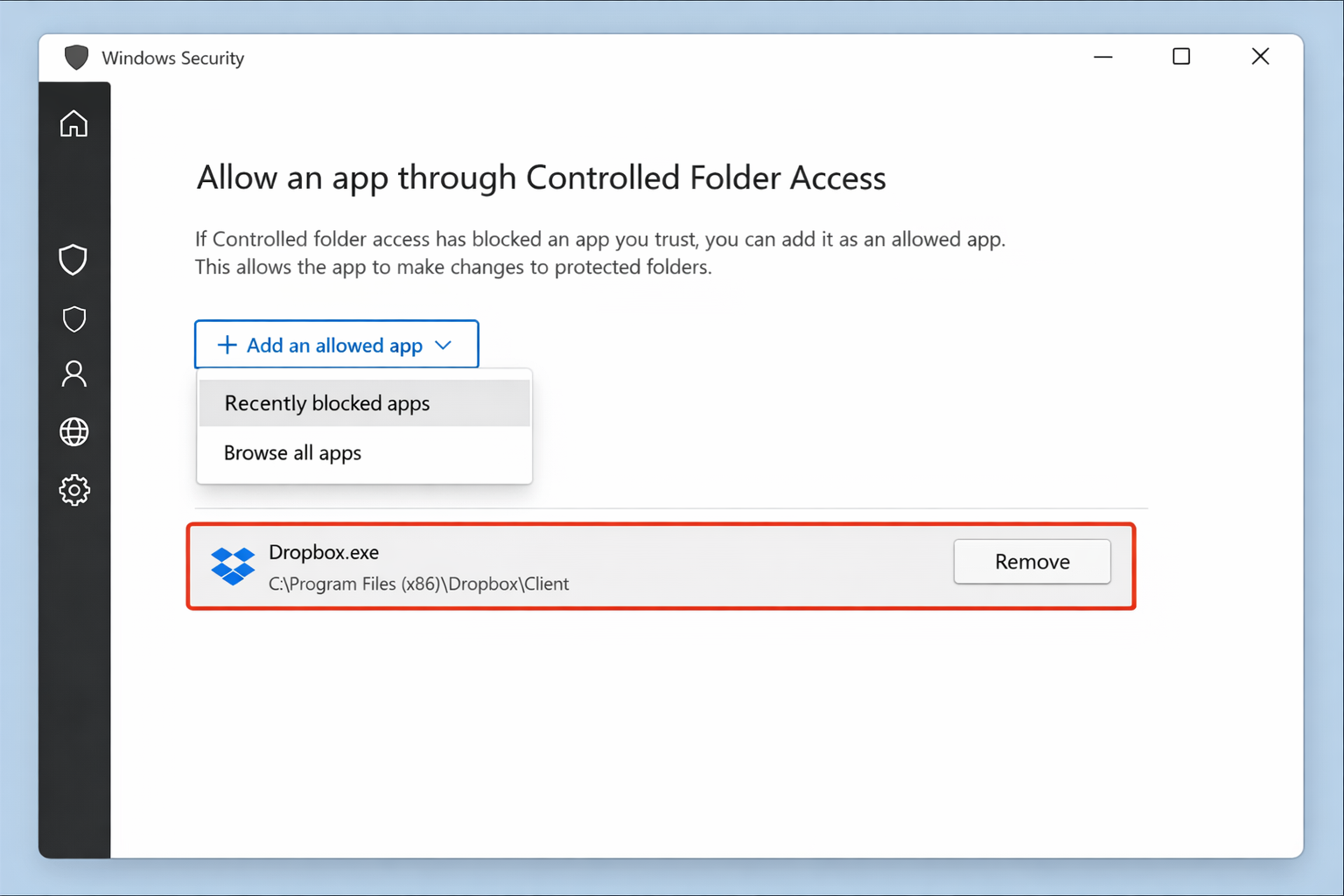
- When Controlled Folder Access blocks a legitimate app, and it will, Windows will notify you. Return to this allowlist panel, click + Add an allowed app > Recently blocked apps, and add the app you trust.
Expect to allowlist a few applications in the first day or two. File indexing tools, backup software, and some productivity apps commonly trigger blocks. It’s slightly annoying at first, but manageable.
Limitation: Controlled Folder Access is a meaningful additional layer, not a complete fix. Sophisticated malware with deeper system access may work around it. Don’t skip Fix #4 or Fix #5 if your risk profile calls for those.
Which Fix Is Right for Your Situation
| Your Profile | Recommended Fixes |
|---|---|
| Single-user PC, good security hygiene, no sensitive work data | Fix #1 + Fix #3 (periodic cleanup) |
| Single-user PC, want Recall on, want extra protection | Fix #1 + Fix #3 (regularly) + Fix #6 |
| Shared PC or shared Windows account | Fix #4 + Fix #3 (delete existing history) |
| Sensitive professional data (legal, medical, financial, HR) | Fix #4 + Fix #3 + Fix #5 |
| Uncertain about recent downloads or phishing exposure | Fix #3 immediately, then Fix #4 |
| Technically confident, want Recall on with maximum protection | Fix #1 + Fix #2 (during sensitive tasks) + Fix #3 (regularly) + Fix #6 |
Wrapping Up
Windows Hello encryption genuinely protects your Recall data from thieves, remote attackers, and other accounts on the same PC. It doesn’t re-authenticate every program that runs under your account once you’re already logged in. That’s the gap TotalRecall Reloaded demonstrated.
For most single-user home PCs with solid security hygiene, Fix #1 and periodic history deletion via Fix #3 get you most of the way there. Shared PCs or machines with sensitive work data need Fix #4 paired with Fix #5.
Official resources:

