Whether on your own system or in crime dramas with a cybersecurity element, you’ve no doubt heard the term “firewall.” Your firewall is an important part of your computer’s security and helps keep out unwanted connections, potential hackers, and more.
There are different kinds of firewalls and network security. To understand how to best protect your personal data, you need to first know what a firewall is and what it’s intended for.
What Is a Firewall?
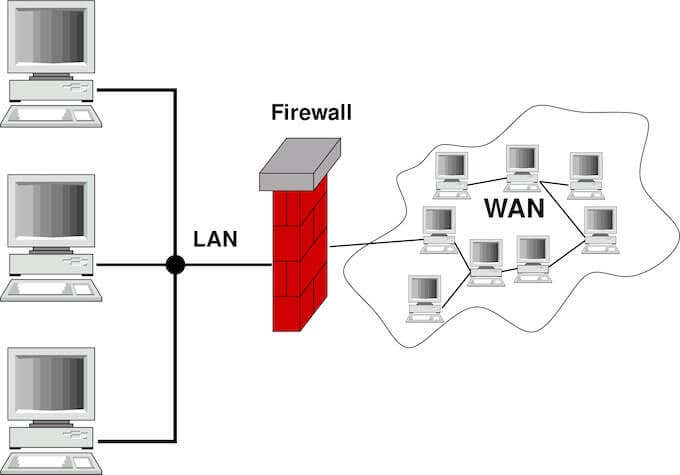
Firewalls are named for the interior walls found in many connected homes that prevent fire from moving through spaces from one home to the next. In much the same way, your computer’s firewall keeps an eye on the traffic in your network and blocks unauthorized connections.
The term first appeared in the 1983 movie WarGames, well before it was ever used in actual computing. While it’s not clear the first time the term was used officially, it’s easy to see the evolution of the term.
In the late 80s, network security routers could filter information as an early form of network security. Since that time, multiple types of firewalls have emerged, each of which serve a different purpose with regard to cyber security.
Types of Firewalls
There are essentially six different types of firewalls. All firewalls are either software-based or hardware-based firewalls. Most of the types mentioned below basically just depend on how the firewall rules and features work, either in software or in hardware.
Virtual Firewall
A virtual firewall is also known as a cloud firewall. This is a type of network protection used within a “virtual” environment, such as the cloud or within a virtualized machine. These firewalls work much like hardware firewalls, but are able to be more thoroughly customized to fit the application.
A virtual firewall can be highly application-specific, in that it can work for one specific application and nothing else. In other uses, it can protect a cloud environment from unauthorized traffic. For example, a service like DropBox or iCloud would use a virtual firewall to protect against intrusion.
Proxy Firewall
A proxy firewall is an earlier, more primitive type of firewall that lacks the more advanced features of more modern network security solutions. In most cases, a proxy firewall protects traffic between point A and point B with basic filters.
A proxy firewall will monitor both incoming and outgoing traffic and block any connection that isn’t allowed. In more technical terms, a proxy firewall blocks connections at the application layer, rather than the network or transport layer.
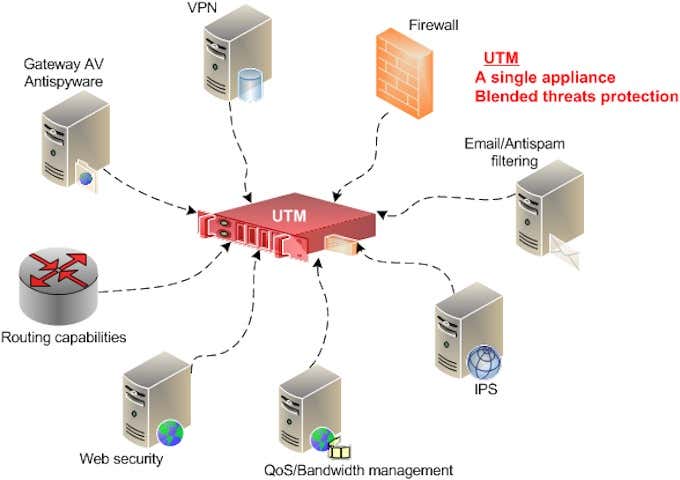
Unified Threat Management Firewall
A Unified Threat Management Firewall, or a UTM firewall, combines firewall functionality with antivirus software. UTM firewalls protect against more than just unauthorized traffic and monitors for a variety of different threats.
UTM firewalls can also monitor for email-based attacks, as well as for threats borne through remote work. Despite this, UTM firewalls are designed to be easier to use, with more simplified control schemes.
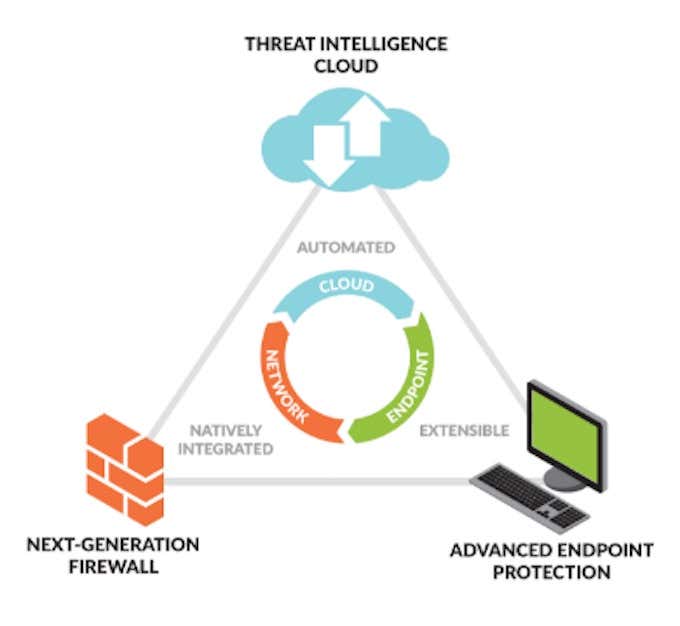
Next-Generation Firewall
A next-generation firewall, or NGFW, is a much more advanced and powerful type of firewall. Where a standard firewall might focus primarily on filtering packets, a NGFW combines that technology with advanced intrusion detection and other features to provide next-level protection.
In some cases, NGFWs utilize artificial intelligence to provide better network security. This allows them to provide significantly more levels of protection, but this kind of firewall tends to be used more often in corporate environments with large networks and databases.
Threat-Focused NGFW
If a NGFW is a more advanced firewall, then a threat-focused NGFW is the most advanced option. It has broad awareness of the network to know where the largest threats lie, and it can respond to potential attacks thanks to intelligent security automations.
Stateful Inspection Firewall
A Stateful Inspection Firewall is the standard type of firewall found on most modern systems and blocks traffic based on the “state” of a connection. This is known as “stateful packet inspection,” or “dynamic packet filtering.”
In other words, a stateful inspection firewall allows only authorized traffic with the correct state to pass through and blocks all other connections. It also monitors threats based on port and protocol type.
Do You Need a Firewall?
In the early days of the Internet, it wasn’t unusual for users to install their own personal firewalls as an added layer of protection against online threats. However, those days are long gone now—not due to lack of threats, but because firewalls are readily available.
Both Windows and macOS provide built-in firewalls in the operating systems that offer a tremendous amount of protection. On top of that, the vast majority of wireless routers also provide another layer of protection in the form of Network Address Translation.
That said, even with a built-in firewall through your operating system, your computer can still be vulnerable on public networks. If you connect to airport Wi-Fi or hop on a public network in a coffee shop, you need more than just a firewall to stop someone with a packet sniffer.
If you routinely use unsecured Wi-Fi networks, consider investing in a virtual private network, or VPN—it encrypts your information and protects it against prying eyes. It’s the only secure way to access banking information or sensitive data while on a public network.
You can install a third-party firewall on your system for added protection, but it isn’t strictly necessary. However, if you want to make sure that your system is protected, we have a list of the best firewalls for Windows 10 that aren’t Windows Defender, the default firewall software.
The topic of firewalls connects heavily to network security and can quickly become a highly technical topic, but the takeaway is this: Firewalls are important, but you probably already have access to multiple firewalls through your OS and your network router. Just remember, if you choose to disable your OS firewall for any reason (like an update or patch), turn it back on after you finish.