There’s a good chance you’ve happened upon this article because an application you’re trying to run is complaining about a “port” being blocked or you’ve read about how leaving certain “ports” open on your network can be a security problem.
Either way, by the end of this piece you’ll not only know what these ports everyone is going on about are, but how to check your computer to find open or closed ports.

What Is a Network Port?
The first thing you should know is that the ports we’re referring to here are virtual. It has nothing to do with the physical network hardware ports on your router, TV, consoles or computers. Ports are simply a way for your network hardware and software to organize information traffic.
Think of reserved lanes on a road. The sidewalk is for pedestrians. There might be a dedicated bike lane. Carpool vehicles and buses have their own lanes too. Ports serve the same function. One port might be used for receiving emails, while another carries file transfer requests, or website traffic.

There are two common types of ports, which need a brief explanation before we move on to checking which ports on your system are open and which aren’t.
What Are TCP & UDP Ports?
The two common types of ports on modern networks are known as TCP and UDP ports. That is Transmission Control Protocol and User Datagram Protocol respectively. So these two port types use different network protocols.
Which you can think of as distinctive sets of rules for how bits of information should be sent and received. Both port types are built on the fundamental Internet Protocol (IP) that makes the internet and home networks, well, work. However, they are suitable for different applications.

The big difference is that when you send information over UDP, the sender doesn’t first have to establish a connection with the receiver before starting the conversation. It’s a bit like sending a letter. You don’t know if the other person received your message and you have no guarantee that you’ll get any feedback.
TCP, on the other hand, is more like making a phone call. The receiver has to “pick up” the connection and there’s a back-and-forth flow of information until someone deliberately hangs up.
UDP messages are generally broadcast over a network to anyone who is listening on the specified UDP port. This makes it perfect for housekeeping type messages that relate to running the network itself. It’s also perfect for voice-over-IP streaming, online video games and streaming broadcasts.
Why? These applications benefit from UDP’s low latency and constant stream of information that doesn’t have to be perfect to be useful. A little corruption in your Skype chat is far less important than low amounts of lag, after all.
TCP is much more common than UDP and absolutely makes sure that all data is received free from errors. Just about everything that doesn’t need the specific advantages of UDP, uses TCP instead.
Which Ports Are Usually Open By Default?
There are a LOT of ports. A port number can be anything from 0 to 65535! That doesn’t mean any application can just pick any port. There are established standards and ranges, which helps us make sense of the noise.

Ports 0-1023 are associated with some of the most important and fundamental network services. This makes sense, since the lower-numbered ports were assigned first. The SMTP protocol for email, for example, is exclusively used by port 25.
Ports 1024-49151 are known as “registered ports” and are assigned to important common services such as OpenVPN on port 1194 or Microsoft SQL on ports 1433 and 1434.
The rest of the port numbers are known as “dynamic” or “private” ports. These ports aren’t reserved and anyone can use them on a network to support a particular service. The only problem crops up when two or more services on the same network are using the same port.
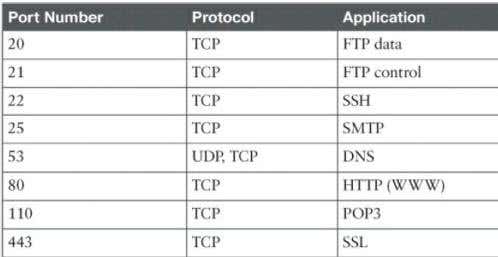
While it’s impossible to list every single important port, these common ports are useful to know by heart:
- 20 – FTP (File Transfer Protocol)
- 22 – Secure Shell (SSH)
- 25 – Simple Mail Transfer Protocol (SMTP)
- 53 – Domain Name System (DNS)
- 80 – Hypertext Transfer Protocol (HTTP)
- 110 – Post Office Protocol (POP3)
- 143 – Internet Message Access Protocol (IMAP)
- 443 – HTTP Secure (HTTPS)
Since there are so many thousands of common port numbers, the easiest approach is to remember the ranges. Which will tell you if a given port is reserved or not. Thanks to Google, you can also look up which services use a specific port in no time at all.
Find Open Ports In Windows

Now that we’ve got all the basic knowledge about TCP and UDP ports out of the way, it’s time to get down to the process of finding which ports are open and in use on your computer.
The good news is that Windows has a pretty useful command built into it that will show you what ports are currently being used on your computer by various applications and services.
- The first thing you want to do is open the Start Menu and search for CMD.
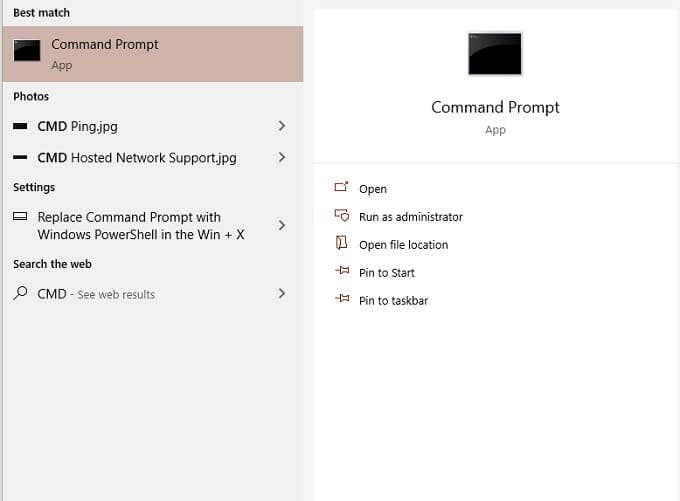
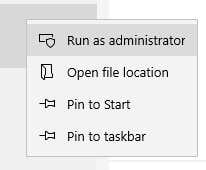
- Now, right-click on CMD and Run as Administrator.
- With the Command Prompt open, type:
Netstat -ab
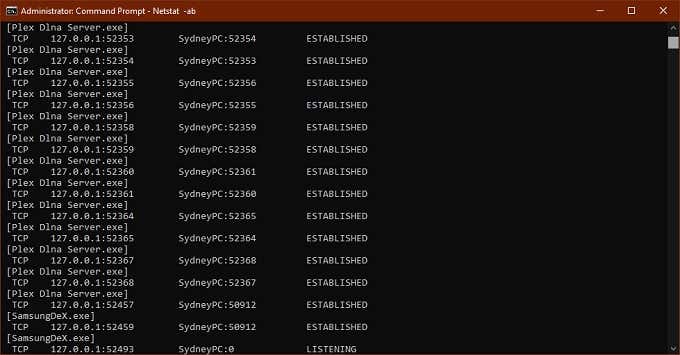
- Don’t worry about a long list of info scrolling by faster than you can read it. You can simply use CTRL+C and CTRL+V to copy and paste the information into Notepad or any other text editor.
- The information in brackets is the name of the program that’s using the port. TCP or UDP refers to the protocol being used on that port. The number consists of an IP address and then the port number after the colon.
Scanning For Blocked Ports
That takes care of finding which ports are being used and by which application, but it doesn’t tell us which ports are being actively blocked by the Windows Firewall.
- Once again, open the Start Menu and search for CMD.
- Right-click on CMD and Run as Administrator.
- With the Command Prompt open, type:
netsh firewall show state
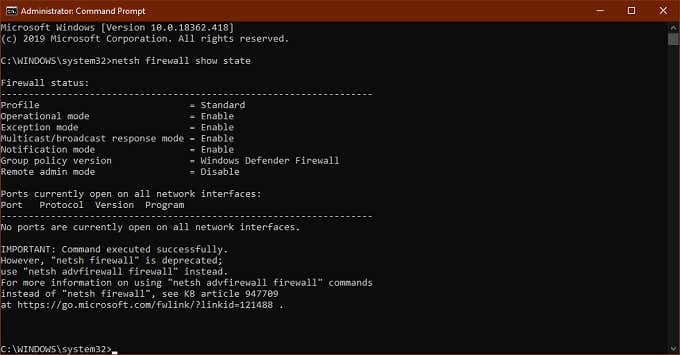
This is a display of blocked and open ports as per the configuration of your Windows Firewall.
You’ll see a note about this command being deprecated, but the new command doesn’t show us the information we want. So for now using the ‘show state’ command is still the fastest and easiest way to get port information.
Just because the Windows Firewall isn’t blocking a port, that doesn’t mean your router or ISP aren’t. So the last thing we want to do is check if any external blocking is happening.
- Open the Start Menu and search for CMD.
- Now, right-click on CMD and Run as Administrator.
- With the Command Prompt open, type:
netstat -ano | findstr -i SYN_SENT
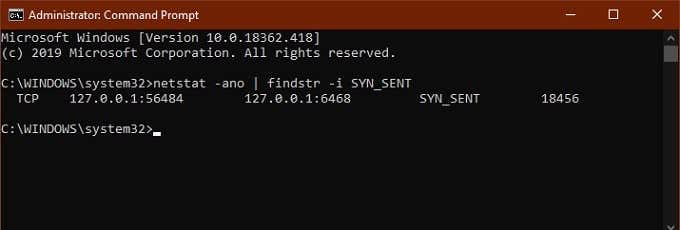
If you don’t get any hits listed, then nothing is being blocked. If some ports are listed, it means they are being blocked. If a port not blocked by Windows shows up here, you may want to check your router or pop an email to your ISP, if switching to a different port isn’t an option.
Useful Apps To Map Out Your Port Status
While the Command Prompt is a good quick and dirty tool, there are more refined third-party applications that can help you get a picture of your port configuration. The two highlighted here are just popular examples.
SolarWinds Free Port Scanner
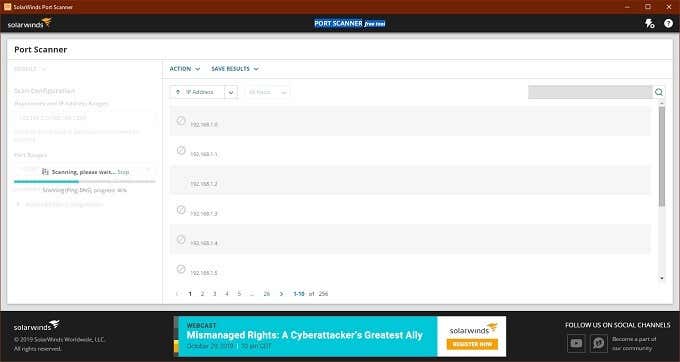
SolarWinds requires that you submit your name and details in order to download it, but it’s up to you whether you put your real information into the form or not. We tried several free tools before settling on SolarWinds, but it was the only tool that both worked properly under Windows 10 and had an easy interface.
It was also the only one not to trigger a false positive virus flag. One of the big problems with port scanning software is that security companies tend to see them as malware. So most users ignore any virus warning that come with such tools. That’s a problem because you can’t tell the difference between a false positive and a real virus in these apps.
SolarWinds might come with some strings attached, but it actually works as advertised and is easy to use.
CanYouSeeMe

This is, as you can probably tell, a website service rather than an application. It’s a good first port of call to see if external data can get through your local port or not. It auto-detects your IP address and all you have to do is specify which port to test.
It will then tell you if the port is blocked or not and you’ll then have to figure out whether the blockage is on the computer, router or at the service provider level.
Conclusion
For most users, ports aren’t something you need to worry about. They are managed by your operating system, applications and network hardware.
When things go wrong however, it’s good to have the tool in hand that let you find open ports to sniff out suspicious activity or figure out where exactly your precious information is hitting a brick wall.