The way a home network usually works is that anyone with your network passphrase can connect to your home network. However, it’s possible to add another layer of security where only specific devices are allowed to connect. This is called MAC address filtering.
Keep in mind however that Mac address filtering isn’t a single security solution. It only serves as an extra level of difficulty for hackers. It’s a layer that they will still be able to break through (see below), but anything that makes things more difficult for hackers is always a good thing.
Why Whitelist Devices?
Your router handles all network traffic inside and outside your home network. It decides whether certain devices are allowed to connect to your home network.
Normally, this access is determined by whether or not the user of the device types in the correct network passphrase. This is the passphrase you configure in the Set Password section under the Security menu in your router.
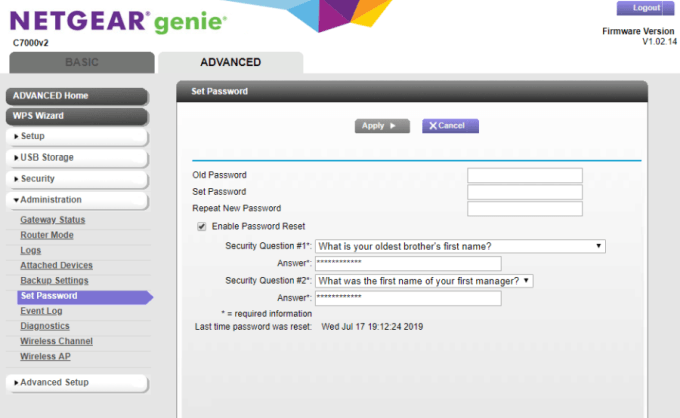
This is the only security barrier stopping a hacker from connecting to your network. If you’ve set up a complex password, that may be enough. Unfortunately, most people set password that are fairly easy to crack using basic hacker tools.
You can add a second layer of security by only allowing specific devices to connect to your home network.
How MAC Address Filtering Works
You can set up your router to only allow specific devices by adding their MAC addresses to the router’s Access Control list.
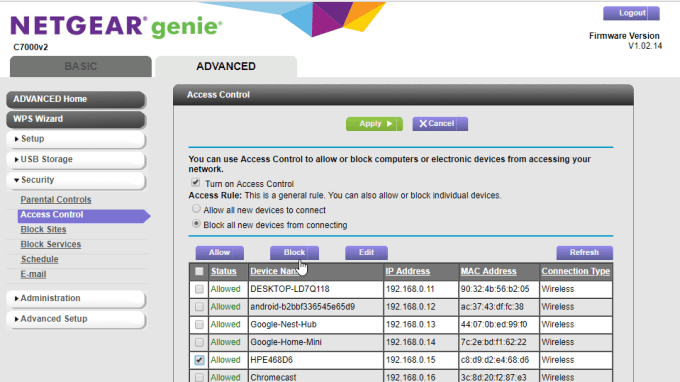
- Usually, you can find this
list by logging into your router and navigating to the Security menu. You’ll find the list of devices under Access Control.
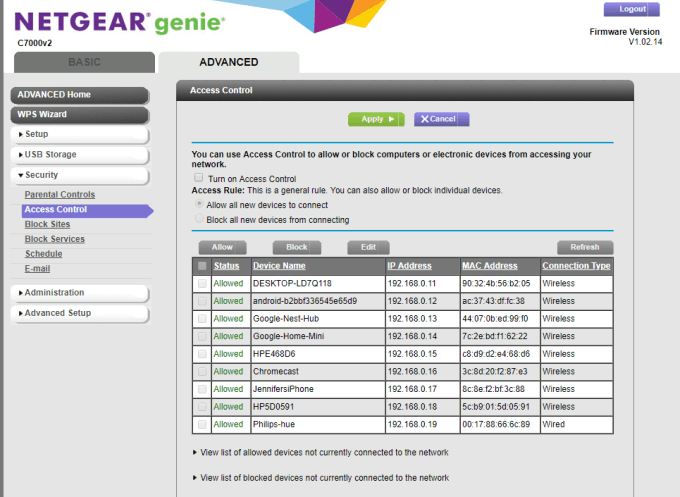
- You can enable the Mac
Address Filtering feature by selecting Turn
on Access Control. - Once this is enabled, you can
then select Block all new devices from
connecting. - Once this is selected, you’ll
be able to select any of the already-connected devices and block them if you
don’t recognize them.
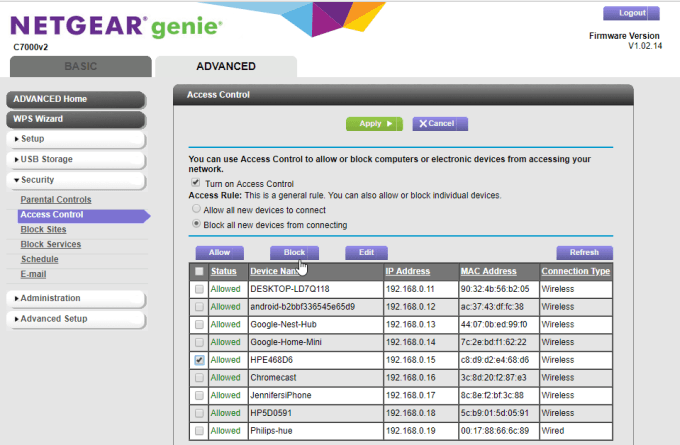
- It’s a good idea while you’re
doing this to scan through the devices and make sure all of the listed devices
and MAC addresses are devices you recognize. - If, later on, you need to add
new devices to the list, you’ll need to change the setting back to Allow all new devices to connect. Then
connect the device to the network using the network password. - Once connected, go back to
the Access Control settings and change the setting back to Block all new devices from connecting.
Some routers will let you enter devices and MAC addresses manually. But to do this, you’ll need to know the MAC address of the computer you’re connecting.
How To Identify The Mac Address Of Your Computer
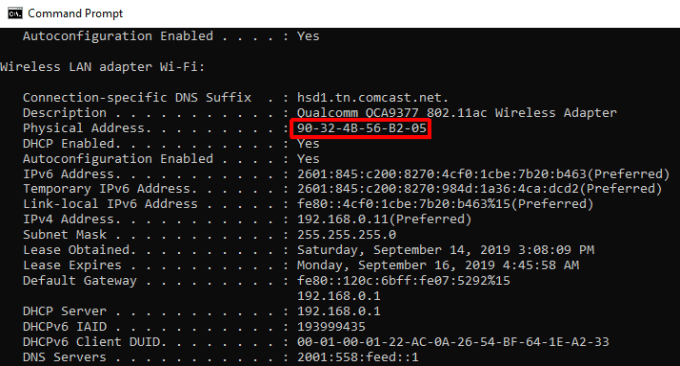
Checking the Mac address on a Windows system is very easy.
- Open the Windows Command
window, type ipconfig /all and press
Enter. - Search through the results
for the network adapter that shows as being connected to a network. - Make a note of the Physical Address listed in that
section. - This physical address is the
same as the connected MAC address shown in your router.
On a MacOS system, the process is slightly different.
- Open System Preferences and select Network.
- Select the connected network
and select the Advanced button. - Select the Hardware tab to see the MAC Address listed at the top.
You can see the procedures above for finding a MAC address on a PC or a Mac, or even on other devices, complete with screenshots and additional details, in this guide on how to determine a MAC address.
For devices like Google Home, Alexa, Philips Hue lights, or other smart home devices, you can usually find the MAC address printed on the label underneath the device. This is usually the same label where you’d find the serial number.
Once you have the MAC addresses for all of the devices that need to whitelist, you can then log into the router and either make sure they’re already connected, or add the MAC address to the existing list.
How Hackers Beat MAC Address Filtering
There are a lot of ways hackers can break through your various tactics to secure your Wi-Fi and home network. Hackers also have a way to get through MAC address filtering as well.
Once a hacker recognizes that they’re blocked from accessing your network via MAC address filtering, all they have to do is spoof their own MAC address to match one of the addresses you’ve allowed.
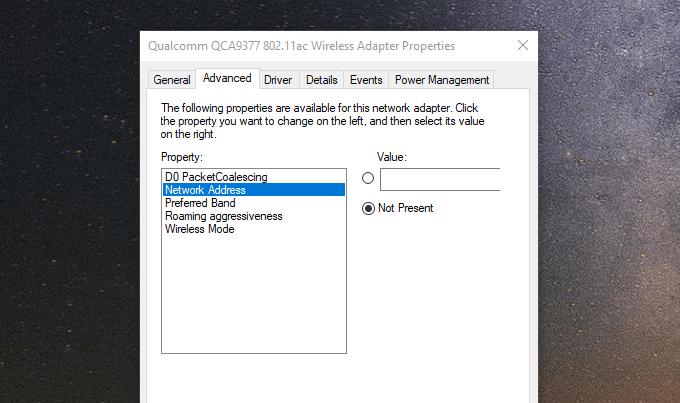
They do this by:
- Going into Network and Sharing Center in the
Control Panel. - Selecting Change adapter settings.
- Selecting the Properties of their network adapter and
the Configure button. - Selecting Network Address and filling in the Value field with the desired MAC
address.
That’s the easy part. The difficult part is that the hacker will also need to use a packet sniffing tool to pull existing MAC addresses currently communicating on your network. These software tools are not always easy for amateurs to use, and can take effort to use correctly.
Other tech sites may tell you that since hackers can do this, then it’s not worth using MAC address filtering at all. But that’s not entirely true. If you don’t use MAC address filtering:
- You aren’t even blocking
non-hackers or amateur Wi-Fi thieves from your network. - You’re avoiding an easy layer
of security for no good reason. - You aren’t trying to make
getting onto your network as difficult as possible with multiple layers of
complexity. - You won’t have access to a
simple tool that can help with parental internet controls.
This is why it’s a good extra layer of protection for your network, but you shouldn’t depend on it as your only source of protection. Whitelisting specific devices should be used as just one part of your overall arsenal of network protection.