RFID or Radio-Frequency Identification technology is everywhere. Employee ID cards, on items you buy at a store and even inside our pets. It’s a simple yet ingenious technology that is coming into its own in a world where everything is increasingly digitized. Quite impressive for a technology that’s been in use since World War II.
Which makes this a great time to familiarise yourself with what RFID is and the various uses it’s used for today.
The Physical Components Of RFID
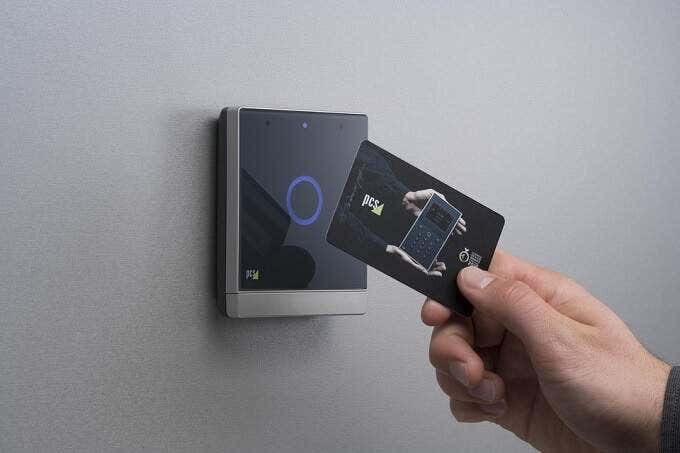
An RFID system consists of two main components. First, you have the RFID tag itself. This contains the ID information, usually with reference to a large external database. Secondly, we have the RFID reader. This is the device that extracts the information stored in the RFID tag.
Since this technology uses radio waves to send and receive information, both tags and readers need some form of antenna to work.
RFID tags consist of an integrated circuit and an antenna. In other words a microchip that has the electronic components inside it. The integrated circuit is connected to a tiny antenna. These components are common to all RFID tags, but they vary wildly in size, shape and appearance. Depending on what they are to be used for.

For example, employee ID cards that are used to open doors layer the RFID between sheets of plastic. When inserted into living creatures, the RFID chip sits inside a biologically neutral glass capsule. To name but two approaches.
The Data Inside RFID Chips
RFID tags have very little storage space. Most tags only have enough room for 96 bits. Although as many as 2000 bits is possible.
Consider that the extended ASCII character set uses eight bits per character, and there isn’t much room. With the available space, it’s possible to store something like a name or telephone number. However it’s far more common for the data stored inside an RFID chip to reference a record in an external database.
RFID chips also have memory that varies in terms of readability and writability. Most RFID chips are likely to be of the read-only type. Where the data cannot be changed out of the box. Since the RFID’s stored number can be linked to any database entry, this is a popular and cost effective way to use large volumes of RFID tags. It also helps that the serial numbers are unique and can’t be tampered with. This is the sort of tag you’ll find on pill bottles and other mass-produced products.
There are also write-once cards, also known as “field programmable” RFID chips. These chips can have data written to them once, but from then on they can only be read from. These are useful for small-scale applications. Then you have read-write tags, which can be overwritten as needed.
What Are Active vs Passive RFID Tags?
There are two main variants of RFID tag. The one that most people encounter is passive. It has no power source of its own. Instead, it gets energy from the RFID reader via the antenna, which it uses to disgorge its tiny cache of data.
The advantages of passive RFID tags are many. Since it requires no maintenance or power, they can be permanently embedded in objects. This makes it easy to protect them from harm or to hide them.
The downside is that passive tags have a shorter range than active tags. Which have an internal power source that allows them to broadcast their signal constantly or at set intervals. RFID technology uses very little power, so even active units can run for a significant amount of time without needing a recharge or a new battery.
RFID Frequencies
RFID tags operate in a number of different frequency bands:
- Low-frequency: 30Khz – 500 Khz. These tags have very short ranges, usually only inches.
- High-frequency: 3MHz – 30MHz. These tags range from inches to feet.
- Ultra-high Frequency: 300Mhz – 960 MHz. An average 25-foot range.
- Microwave Frequency: 2.45GHz, with ranges over 30 feet.
Passive tags are usually either Low- or High- Frequency, with the Ultra-high and Microwave Frequency tags needing active power to work.
RFID & Smartphone NFC

Many newer, higher-end models of smartphone have a feature known as “NFC” or near-field communication. This is a wireless communications feature that uses the same protocol (essentially the language) as RFID.
The big difference here is that NFC devices can be used as both an RFID reader and can simulate RFID tags. There are all sorts of uses for this, with “tap and pay” contactless mobile payments being a prime example. Two NFC devices can also send data to each other if they are close enough to touch.
NFC is not a universal RFID system. It only operated on the 13.56Mhz high-frequency RFID band, making it very short range by design.
RFID Blocking

RFID signals can be blocked using the right materials. Since passive tags need to be pretty close to the reader to work, they’ve found use in bank cards. In many countries you can now “tap and pay” on card machines. This has also led to a new form of crime, where small amounts of money can be stolen by reading these cards through wallets.
Alternatively,the RFID tag could potentially be copies using a surreptitious reader. NFC technology in smartphones is one way this can be done.
Which is why RFID blocking wallets have now become popular. Cards that contain RFID technology can be stored in a special pouch that prevents the card being read without the owner’s knowledge.
The Many Uses Of RFID

One of the earliest and most useful uses of RFID technology was tracking livestock. Now it’s also used extensively to track products, components and any other movable items. RFID technology can track an item from where it is made to where it is sold.
RFID is, as mentioned above, used in bank cards, smart cards and various authentication systems. With the rise of the internet of things (IoT) it’s also becoming an essential part of the digitization of physical objects.
Pets and some humans are also being injected with RFID tags. In the case of pets, it’s a way to recover lost animals. In humans they may also have medical applications, since some RFID systems can also include sensors.
RFID, or something like it, is almost certain to play a major role in giving real-world objects and entities a digital identity. As everything becomes more automated, it’s the only real way to make sure we know where everything is and what’s happening to it.